Secureworks Red Cloak High Cpu
Secureworks Red Cloak High Cpu - The steps below show how to confirm that dell encryption is the cause of the high cpu usage in system process. Its pretty invasive for a personal laptop lol. Netflow, dns lookups, process execution, registry, memory. Hi, hope this is the right. The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. What seems to happen is that something triggers high demand and then every process on the computer joins in. During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase. The following table outlines the system resources.
The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. Its pretty invasive for a personal laptop lol. The following table outlines the system resources. Netflow, dns lookups, process execution, registry, memory. What seems to happen is that something triggers high demand and then every process on the computer joins in. Hi, hope this is the right. During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase. The steps below show how to confirm that dell encryption is the cause of the high cpu usage in system process.
Netflow, dns lookups, process execution, registry, memory. The steps below show how to confirm that dell encryption is the cause of the high cpu usage in system process. What seems to happen is that something triggers high demand and then every process on the computer joins in. The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. The following table outlines the system resources. Its pretty invasive for a personal laptop lol. Hi, hope this is the right. During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase.
Secureworks Managed Detection & Response powered by Red Cloak It's
What seems to happen is that something triggers high demand and then every process on the computer joins in. Its pretty invasive for a personal laptop lol. The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. Hi, hope this is the right. Netflow, dns lookups, process execution, registry, memory.
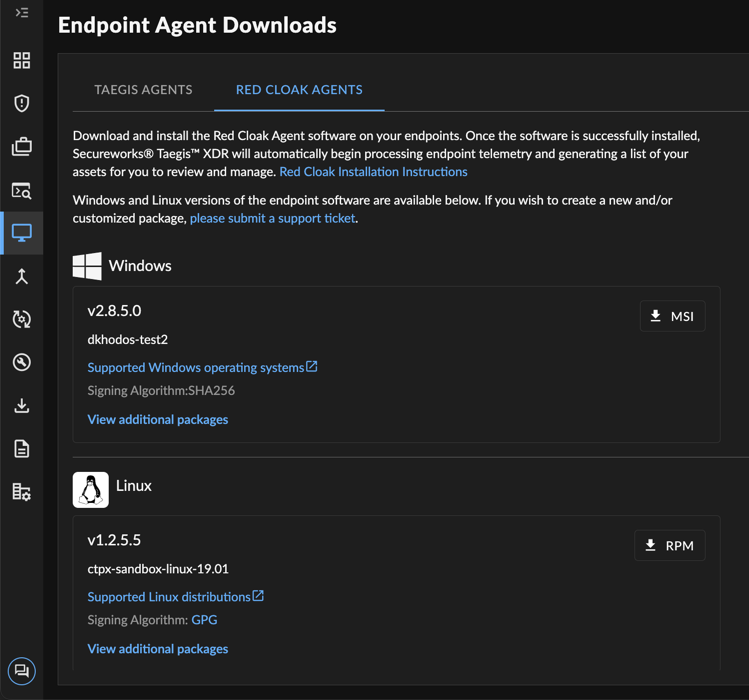
Installation
The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. What seems to happen is that something triggers high demand and then every process on the computer joins in. Netflow, dns lookups, process execution, registry, memory. The steps below show how to confirm that dell encryption is the cause of.
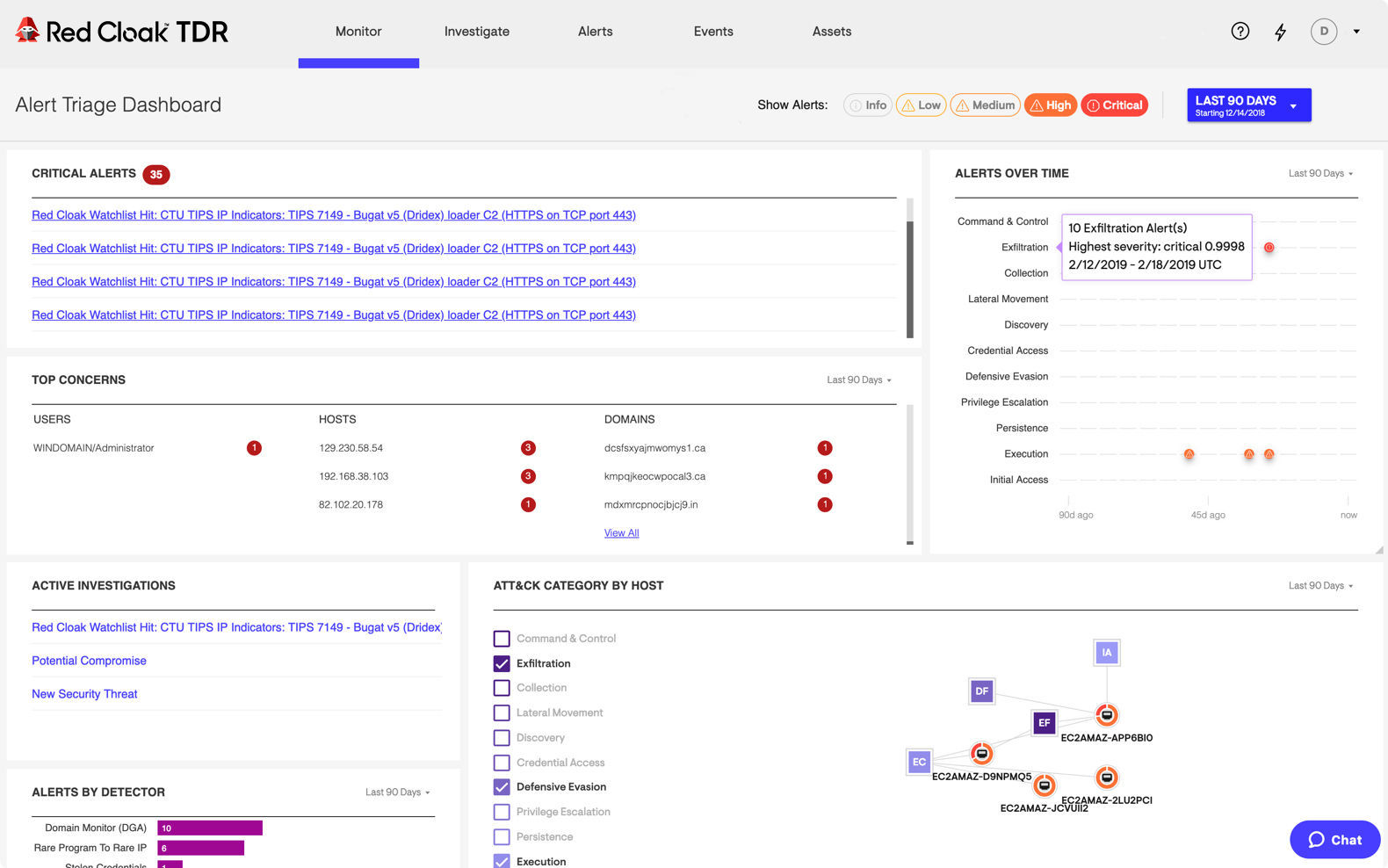
Red Cloak Threat Detection & Response Pricing, Reviews and Features
Netflow, dns lookups, process execution, registry, memory. The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. What seems to happen is that something triggers high demand and then every process on the computer joins in. Its pretty invasive for a personal laptop lol. The following table outlines the system.
Secureworks Launches Red Cloak TDR Cybersecurity Service! Tech ARP
The steps below show how to confirm that dell encryption is the cause of the high cpu usage in system process. Its pretty invasive for a personal laptop lol. The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. What seems to happen is that something triggers high demand and.
Premium Photo A woman in a red dress with a red cloak.
The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. Netflow, dns lookups, process execution, registry, memory. The steps below show how to confirm that dell encryption is the cause of the high cpu usage in system process. The following table outlines the system resources. Hi, hope this is the.
Premium AI Image a woman in a red cloak with a red cloak on her head
The steps below show how to confirm that dell encryption is the cause of the high cpu usage in system process. During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase. The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. Hi, hope this.
Introducing Red Cloak Threat Detection and Response We're
The following table outlines the system resources. Netflow, dns lookups, process execution, registry, memory. The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. Hi, hope this is the right. What seems to happen is that something triggers high demand and then every process on the computer joins in.
secureworks red cloak React Milk
The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase. The following table outlines the system resources. Netflow, dns lookups, process execution, registry, memory. The steps below show how to confirm that dell encryption.
Generated Ai Red cloak with blood splatters, on Transparent Background
During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase. What seems to happen is that something triggers high demand and then every process on the computer joins in. The following table outlines the system resources. The steps below show how to confirm that dell encryption is the cause of the high cpu usage.
A Girl in a Red Cloak Walks through the Night Forest Stock Image
During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase. Hi, hope this is the right. Its pretty invasive for a personal laptop lol. The steps below show how to confirm that dell encryption is the cause of the high cpu usage in system process. The red cloak endpoint agent communicates with the cluster.
The Following Table Outlines The System Resources.
The red cloak endpoint agent communicates with the cluster over port 443 using tls v1.2 with a strong cipher suite. What seems to happen is that something triggers high demand and then every process on the computer joins in. Hi, hope this is the right. Its pretty invasive for a personal laptop lol.
The Steps Below Show How To Confirm That Dell Encryption Is The Cause Of The High Cpu Usage In System Process.
During periods of scanning, cpu usage by the red cloak endpoint agent is known to increase. Netflow, dns lookups, process execution, registry, memory.